
What is Penetration Testing? The Ultimate Guide to Ethical Hacking

At its core, penetration testing (often referred to as a pen test) is an authorized, systematic security assessment where professionals actively attempt to exploit vulnerabilities within your IT infrastructure, applications, or personnel. Relying solely on automated defensive tools leaves organizations blind to complex attack vectors. Through the practice of ethical hacking, experts move beyond simple scanning, using industry frameworks like OWASP and NIST to bypass firewalls, inject payloads, and uncover the hidden logical flaws that software scanners inherently miss.
The primary goal is to safely simulate a real-world cyberattack to determine exactly how far a malicious actor could breach your systems, whether that means extracting sensitive data or gaining domain admin privileges. By chaining together minor misconfigurations, testers demonstrate how a tiny crack can lead to a massive data compromise. Ultimately, this hands-on exercise provides empirical proof of where your defenses fail, delivering a clear, actionable roadmap to patch critical flaws and optimize your cybersecurity budget before a genuine threat actor strikes.
Vulnerability Scanning vs. Penetration Testing: Know the Difference
One of the most common SEO searches and points of confusion in cybersecurity is the difference between a vulnerability assessment and a penetration test.
Many organizations believe they are getting a penetration test when, in reality, they are just paying for an automated scan. While both are essential components of a robust cybersecurity strategy, they serve entirely different purposes.
Here is a breakdown of how they compare
Feature | Vulnerability Scanning | Penetration Testing |
Primary Goal | Identify and log known security flaws. | Actively exploit flaws to simulate a breach. |
Approach | Automated software checks. | Manual, human-driven ethical hacking. |
Depth of Analysis | Surface-level ("The door is unlocked"). | Deep-dive (Extracting the data inside). |
Frequency | Continuous or weekly. | Annually, or after major updates |
False Positives | High (lacks environmental context). | Near Zero (flaws are actively proven). |
Final Output | Automated list of missing patches. | Contextual report with remediation steps. |
The 5 Phases of a Penetration Test
A professional ethical hack isn't just a chaotic attempt to break things; it follows a strict, systematic methodology (such as PTES, NIST SP 800-115, or OWASP) to ensure comprehensive and safe coverage.
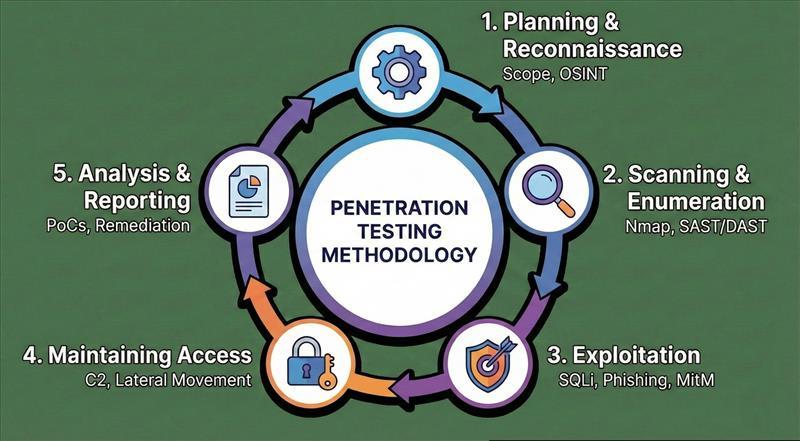
1. Reconnaissance and Planning
This is the intelligence-gathering phase. Before firing a single exploit, testers define the scope, Rules of Engagement (RoE), and goals with stakeholders. They then gather Open-Source Intelligence (OSINT) about the target. They will map your digital footprint by analyzing domain names, sweeping public code repositories (like GitHub) for hardcoded API keys, and searching the dark web for leaked employee credentials.
2. Scanning and Enumeration
Next, the tester actively interacts with the target to identify live hosts, open ports, and running services. This typically involves:
- Network Scanning: Using tools like Nmap to map the internal or external network topology.
- Static Analysis (SAST): Inspecting an application's source code at rest to find vulnerabilities.
- Dynamic Analysis (DAST): Inspecting an application’s code in a running state to spot real-time flaws.
- Fuzzing: Feeding malformed or unexpected data into application inputs to force a crash or reveal hidden errors.
3. Exploitation (Gaining Access)
This is where the actual "hacking" occurs. Using the enumeration data, testers manually exploit vulnerabilities to breach the perimeter. Common attack vectors include:
- Web Application Attacks: SQL Injections (SQLi), Cross-Site Scripting (XSS), and Server-Side Request Forgery (SSRF).
- Network Attacks: Man-in-the-Middle (MitM) attacks, Kerberoasting, or passing-the-hash in Active Directory environments.
- Social Engineering: Launching targeted spear-phishing campaigns against employees to steal login tokens.
4. Post-Exploitation (Maintaining Access)
Once inside, the goal shifts to understanding the business impact. Testers attempt to establish a persistent backdoor (simulating how APTs stay hidden for months) using Command and Control (C2) frameworks. They will attempt to escalate privileges from a standard user to a Domain Administrator, moving laterally across the network to locate your "crown jewels" such as financial databases, PII (Personally Identifiable Information), or source code.
5. Analysis and Reporting
The final and most crucial step. A successful pen test is only as good as its report. The security team compiles a detailed document that translates technical jargon into actionable business intelligence. A high-quality report includes:
-
An executive summary of business risks and potential financial impact.
-
A technical breakdown of every exploited vulnerability, complete with CVSS (Common Vulnerability Scoring System) scores.
-
Proof of Concept (PoC) walkthroughs.
-
Remediation guidance prioritizing exactly how to patch the flaws.
Target Environments: What Should You Test?
Search intent for penetration testing often revolves around what exactly can be tested. Pen tests are categorized by the target environment:
- Network Penetration Testing: Focuses on identifying flaws in your network infrastructure, including firewalls, routers, switches, and servers. This is split into External (public-facing assets) and Internal (simulating an insider threat or breached endpoint)
- Web Application Testing: A deep dive into the coding flaws of your web portals, eCommerce sites, and SaaS platforms, largely guided by the OWASP Top 10.
- Cloud Penetration Testing: Assessing the configuration and security of cloud environments (AWS, Azure, GCP). This focuses heavily on Identity and Access Management (IAM) flaws, misconfigured S3 buckets, and container (Kubernetes/Docker) escapes.
- API Penetration Testing: APIs are the glue of the modern web. Testers look for broken object-level authorization (BOLA) and rate-limiting failures that allow attackers to scrape data.
- Physical Penetration Testing: Testers attempt to physically bypass your office security, tailgating employees, cloning RFID badges, or plugging rogue devices directly into your corporate LAN.
The "Box" Testing Methodologies
Depending on your security maturity, penetration tests are structured by how much information the tester is given upfront.
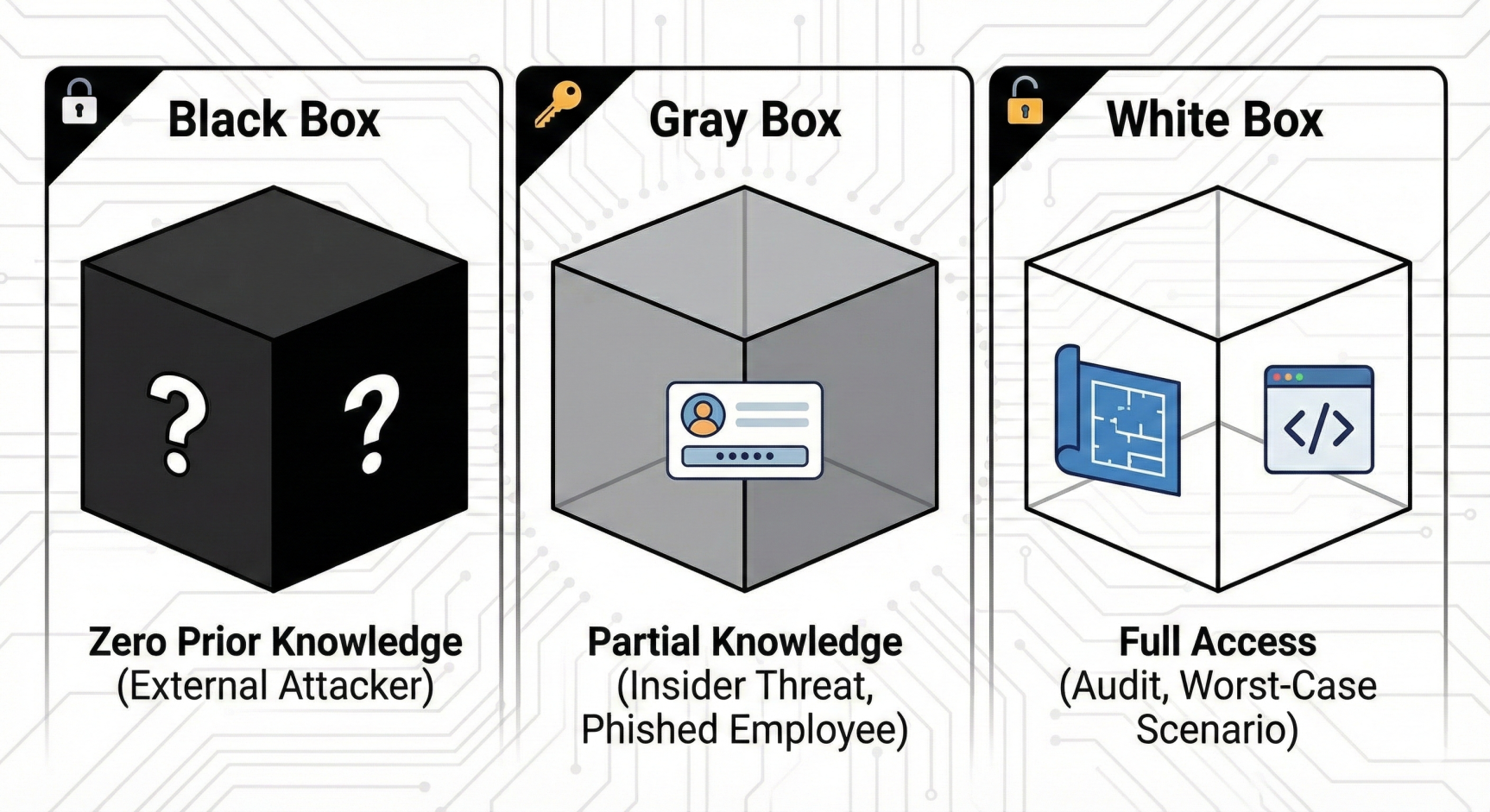
Testing Type | Knowledge Level provided to Tester | The Scenario It Simulates | Best Used For |
Black Box | Zero prior knowledge (IPs or domains only). | An external, unauthenticated hacker starting from scratch. | Testing incident response times, perimeter defenses, and public apps. |
Gray Box | Partial knowledge (e.g., standard user credentials, architecture diagrams). | An insider threat, or an attacker who has successfully phished a low-level employee. | Assessing privilege escalation, internal lateral movement, and tenant isolation. |
White Box | Full transparency (source code, admin access, infrastructure maps). | The ultimate worst case scenario; highly thorough vulnerability hunting. | Rigorous audits, testing custom cryptography, and pre-release software checks |
Why is Penetration Testing Critical? (Compliance & ROI)
Beyond simply preventing a catastrophic data breach, penetration testing is a fundamental business requirement for several reasons: Meeting Regulatory Compliance: Most major data security standards mandate regular pen testing. If you process credit cards, PCI-DSS requires it. If you handle healthcare data, HIPAA demands rigorous risk assessments. If you are a B2B SaaS company, passing a SOC 2 Type II audit almost universally requires an annual penetration test. Protecting Brand Reputation: The average cost of a data breach is in the millions. The cost of a penetration test is a fraction of the cost of losing customer trust, facing regulatory fines, and suffering downtime. Validating Security Controls: You spend thousands on Firewalls, EDR, and SIEM tools. A pen test is the only way to verify that those tools are properly configured and actually catching malicious behavior
Frequently Asked Questions (FAQ)
Most standard penetration tests take between 1 and 3 weeks, depending on the size and complexity of your network or web application.
No. Professional ethical hackers use highly controlled, safe methodologies to test your defenses without disrupting your day to-day business operations.
Yes. Cybercriminals frequently target small and medium-sized businesses (SMBs). Furthermore, many B2B contracts and compliance frameworks (like PCI-DSS and SOC 2) require annual testing regardless of company size.
The Bottom Line: How Often Should You Test?
Cyber threats are constantly evolving. As a general industry standard, organizations should conduct comprehensive penetration tests at least once a year. However, you should also schedule tests immediately following:
- Major upgrades or modifications to your network infrastructure.
- The launch of a new application or a significant feature release.
- The application of major security patches.
- Office relocations or the addition of a new physical site.
A reactive security posture is no longer viable. By aggressively and safely simulating attacks on your own infrastructure, you can patch the holes in your digital ship long before you ever take on water.
















