
Architecting DevSecOps: A Technical Guide to Integrating Security into CI/CD
In the era of cloud-native development and microservices, the traditional "waterfall" approach to security, where testing occurs as a final gate before production, is obsolete. DevSecOps has emerged as the modern solution to this challenge, ensuring security is no longer treated as a late-stage checkpoint. The velocity required by modern business demands that security be decoupled from manual intervention and re-architected as an integral, automated component of the software factory.
This is the domain of DevSecOps. It is not merely a cultural shift but a technical imperative that bridges the operational gap between rapid delivery and robust risk management. By embedding security controls directly into the CI/CD pipeline, organizations achieve secure software development at scale, ensuring that velocity does not compromise posture.
This article provides a technical breakdown of the DevSecOps lifecycle, the necessary tooling infrastructure, and the architectural best practices required to mature your security program.
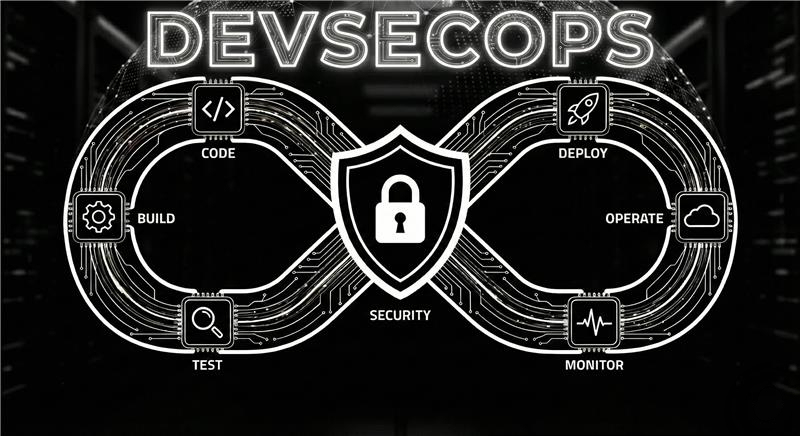
What is DevSecOps?
DevSecOps stands for Development + Security + Operations, and it is a modern approach that integrates security into the software delivery lifecycle from the very beginning. Instead of treating security as a separate phase after development, DevSecOps embeds security controls directly into CI/CD pipelines using automation, secure coding practices, and continuous validation.
In DevSecOps, security becomes a shared responsibility across teams, not only the job of security engineers. Developers, security teams, and operations teams collaborate to identify vulnerabilities early, reduce misconfigurations, protect infrastructure, and ensure applications remain secure in production. This approach enables organizations to deliver software faster while maintaining compliance, reliability, and a strong security posture.
The Technical Imperative: DevOps vs. DevSecOps
To understand the technical necessity of DevSecOps, we must analyze the shortcomings of a pure DevOps model in a high threat environment.
In standard DevOps, the primary metrics are deployment frequency and lead time for changes. Security is often viewed as an external friction point that degrades these metrics. When security findings are presented late in the SDLC, they result in costly rollbacks and "hotfixes" that disrupt the flow.
DevOps vs DevSecOps is fundamentally about refactoring CI/CD security. DevSecOps treats security constraints such as vulnerability thresholds, compliance mandates, and access controls as code. If code fails a security test, the build breaks automatically, just as it would for a failed unit test. This transforms security from a bottleneck into a continuous quality gate.
How DevSecOps Extends DevOps
Feature | DevOps | DevSecOps |
Security involvement | Often late-stage | Integrated from day one |
Testing | Mostly functional | Functional + security testing |
Pipeline | CI/CD | CI/CD + security automation |
Responsibility | Dev + Ops | Dev + Sec + Ops |
Compliance | Manual audits | Automated policy enforcement |
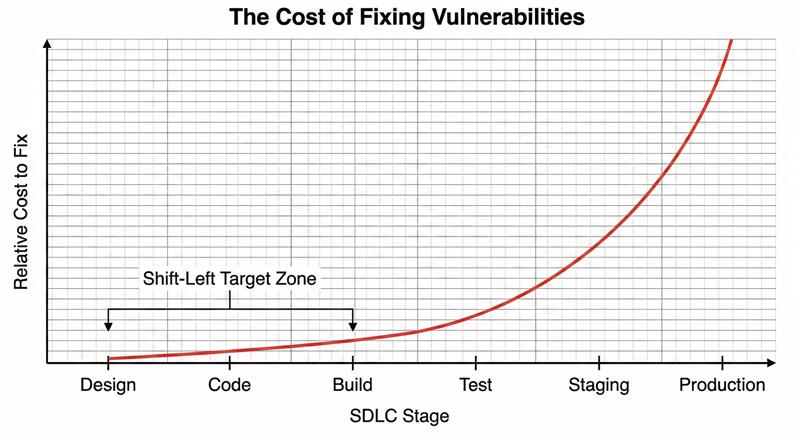
The Core Mechanism: Implementing Shift-Left Security
The defining technical characteristic of DevSecOps is shift-left security.
Traditionally, security testing occurred "right" during staging or production monitoring. Shifting left means moving security analysis to the earliest possible point in the development timeline: the developer's IDE and the initial commit.
The technical goal is to identify vulnerabilities when the cost of remediation is lowest. Fixing a cross-site scripting (XSS) vulnerability detected by an IDE plugin takes minutes; fixing the same vulnerability found during a penetration test of a staging environment requires remoting into Jira tickets, context switching, recompiling, and re-deploying.
Deconstructing the DevSecOps Lifecycle Toolchain
A mature DevSecOps lifecycle is powered by a highly integrated toolchain that automates security gates at every stage of the CI/CD pipeline.
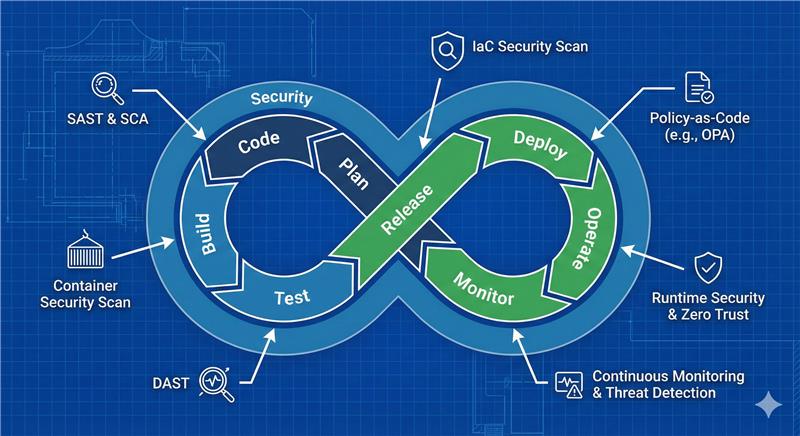
Stage 1: Code & Build (Static and Composition Analysis)
Security begins before the code is even compiled.
- SAST (Static Application Security Testing): SAST tools analyze source code, bytecode, or binaries without executing the application. They hunt for known patterns defined by standards like the OWASP Top 10, such as SQL injection flaws, hardcoded credentials, or buffer overflows.
- Technical Tip: Integrate SAST directly into IDEs via plugins so developers get real-time feedback as they type, and enforce blocking SAST scans upon pull request (PR) submission.
- SCA (Software Composition Analysis): Modern applications consist heavily of open-source libraries. SCA tools scan project dependency files (e.g., package.json , pom.xml ) to identify known Common Vulnerabilities and Exposures (CVEs) in third-party components. They also manage license compliance risks in your supply chain
Stage 2: Test & Stage (Dynamic and Infrastructure Analysis)
Once the application is built and deployed to an ephemeral testing environment, dynamic testing begins.
- DAST (Dynamic Application Security Testing): Unlike SAST’s "white-box" view, DAST takes a "black-box" approach. It executes against a running application, simulating external attacker behavior to discover runtime vulnerabilities like authentication bypasses, session management issues, and server misconfigurations.
- IaC Security (Infrastructure as Code Scanning): In cloud-native environments, infrastructure is defined via tools like Terraform, Ansible, or CloudFormation. IaC security tools scan these configuration files before deployment to detect misconfigurations such as open S3 buckets, overly permissive IAM roles, or unencrypted databases. This is crucial for preventing cloud-based data breaches.
Stage 3: Deploy & Operate (Cloud-Native Security)
Deployment to production requires rigorous security controls tailored for volatile, containerized environments.
- Container Security & Kubernetes Security: Securing the artifact is just step one. You must scan container images (e.g., Docker) for OS-level vulnerabilities in base layers. Furthermore, Kubernetes security is essential for orchestrating these containers securely. This involves enforcing Pod Security Standards (PSS), utilizing Admission Controllers to reject insecure deployments, and locking down RBAC (Role-Based Access Control) within the cluster.
-
Cloud Security and Zero Trust: The surrounding cloud environment must operate under a Zero Trust architecture. This assumes breached perimeters and requires strict identity verification for every service-to-service request, often implemented via service meshes (like Istio or Linkerd) that enforce mutual TLS (mTLS) encryption and fine-grained authorization policies.
Stage 4: Monitor (Continuous Feedback Loops)
Security does not end at deployment.
- Continuous Security Monitoring: This involves aggregating logs from applications, infrastructure, and security tools into SIEM or SOAR platforms. The goal is to detect anomalous behavior indicating a breach in real-time.
- Vulnerability Management: DevSecOps generates massive amounts of data. Effective vulnerability management requires automated tools to deduplicate findings, prioritize them based on threat intelligence and asset criticality, and automatically route them to developer ticketing systems (like Jira)
Advanced DevSecOps Best Practices
To move from "doing DevOps with security tools" to true DevSecOps, adopt these technical best practices:
- Total Security Automation: Manual security reviews cannot scale with multiple deployments per day. Every scan, SAST, DAST, and container checks must be triggered automatically via CI/CD webhooks. If it’s not automated, it doesn't exist in the pipeline.
- Policy-as-Code for Compliance Automation: Instead of manual audits, express compliance requirements (e.g., PCI-DSS, HIPAA) as code using frameworks like Open Policy Agent (OPA). This allows for compliance automation, where every deployment is automatically validated against regulatory guardrails before it can proceed.
- Guardrails Over Gatekeepers: Shift from a "security team approval" model to a "paved road" model. Provide developers with pre-approved, secure infrastructure templates and libraries. If they stay within these guardrails, deployment is fast. If they deviate, automated checks trigger a deeper review.
Conclusion
DevSecOps is a complex technical undertaking that requires rethinking how software is built, tested, and operated. By rigorously applying shift-left security principles, integrating a robust stack of DevSecOps tools like SAST, SCA, and DAST, and automating governance through IaC and policy-as-code, organizations can reconcile the demands of speed and security. The result is a resilient, defensible delivery pipeline that turns security into a competitive advantage.
Want to implement DevSecOps the right way with automation, policy-as-code, and secure cloud deployments? AS13.AI helps teams integrate security into CI/CD pipelines and scale secure delivery across cloud and Kubernetes environments.














