
What is Endpoint Management? The Complete 2026 IT Guide

At the foundation of modern IT operations, endpoint management is the structured approach to authenticating, monitoring, and securing every device that connects to a corporate network. It functions much like an air traffic control system for your infrastructure, confirming the identity of each device requesting access, guiding it to the appropriate network segment, continuously assessing its health, and ensuring software updates and compliance standards are maintained.
Beyond basic oversight, it provides centralized visibility and control across distributed environments, whether on-premises, remote, or cloud-based. By automating policy enforcement and security configurations, endpoint management reduces operational risk while enabling IT teams to scale efficiently and respond proactively to emerging threats.
Endpoints are no longer just desktop towers sitting in a cubicle. Today, an endpoint is any physical or virtual device that exchanges data with your network. This includes:
- Laptops and desktop computers (Windows, macOS, Linux)
- Mobile devices (iOS, Android)
- Servers and virtual machines
- Cloud-native workstations
- Internet of Things (IoT) devices, such as connected security cameras or smart thermostats
Without a centralized strategy to manage these devices, IT teams are left flying blind, relying on manual processes that are virtually impossible to scale and ripe for human error.
Why Endpoint Management Matters for Modern IT
We live in a distributed world. With teams working from home, coffee shops, or corporate offices, the attack surface has expanded exponentially.
- Ransomware and Data Breaches: Endpoints are the most common entry points for threat actors. A single unpatched laptop or a compromised set of credentials can lead to a devastating network-wide breach.
- Regulatory Compliance: Frameworks like GDPR, HIPAA, and the DPDP Act require strict controls over how sensitive data is accessed and stored. Endpoint management provides the audit trails and encryption enforcements necessary to prove compliance.
- Operational Efficiency: Manual patching is a drain on IT resources. By automating updates and configurations, your sysadmins can focus on strategic infrastructure improvements rather than chasing down individual users to click "update."
- Shadow IT and BYOD: Employees often use personal devices (Bring Your Own Device) or unsanctioned software to get their jobs done. Proper management enforces boundaries, containerizing corporate data so it remains secure even on an employee-owned phone.
How Endpoint Management Works: The Architecture
Understanding the mechanics of endpoint management helps clarify why it's so critical. Modern solutions operate on a client server architecture, typically delivered via the cloud (SaaS) for maximum reach and scalability.
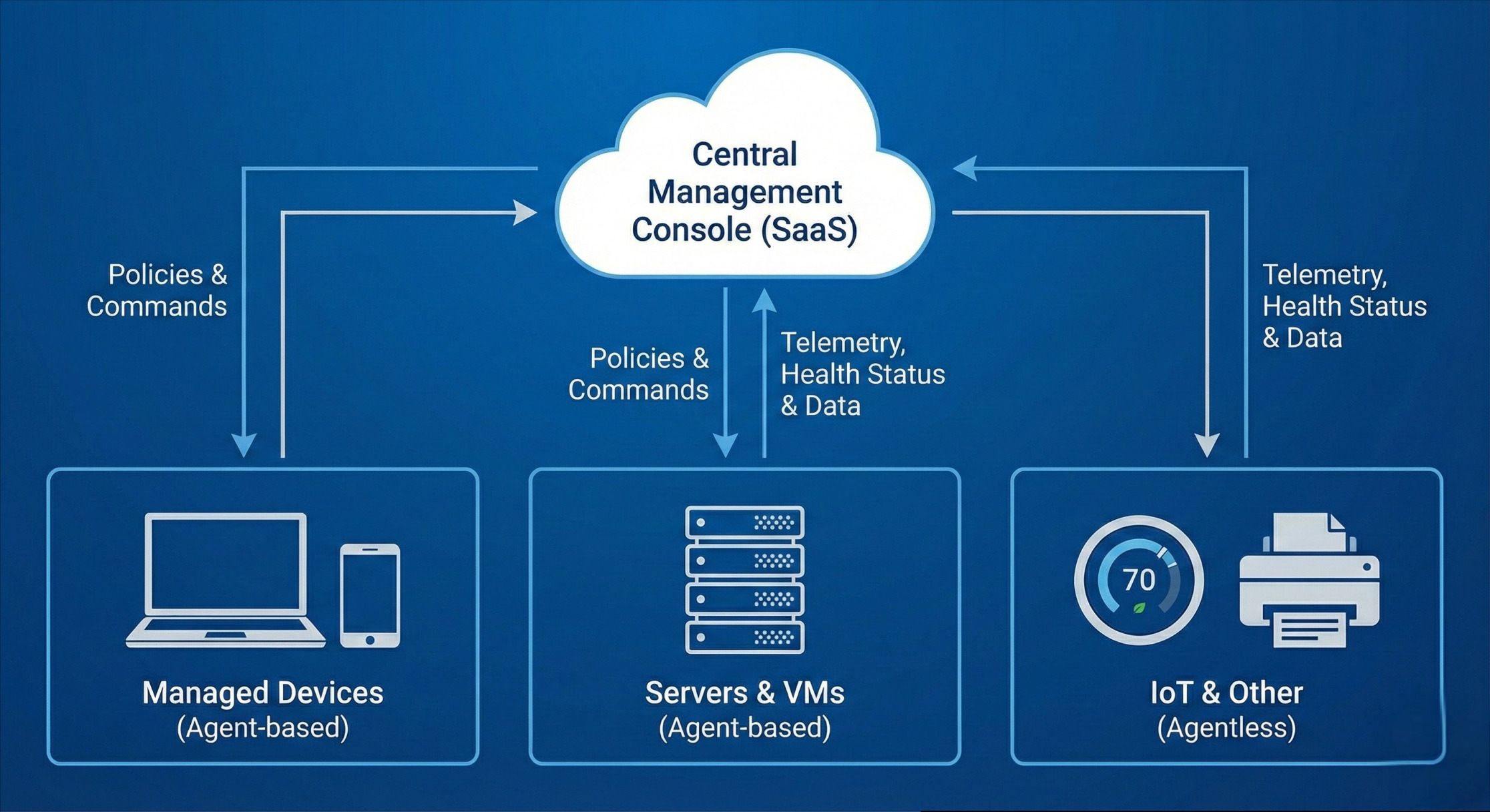
Here is how the data flows and control is maintained:
-
The Central Management Console: This is the single pane of glass for the IT team. Hosted on-premises or in the cloud, this dashboard allows administrators to define security policies, monitor device telemetry, and deploy software across the globe.
- The Endpoint Agent: Most solutions require a lightweight software agent installed on the target device. This agent runs in the background, continuously collecting data (OS version, installed software, hardware health, user behavior) and communicating back to the central console. It also executes commands from the console, such as locking a device or running a script.
- Agentless Management: For devices where installing an agent is impossible (like certain IoT devices or network printers), management is achieved through network scanning, Active Directory integrations, and API connections to monitor traffic and enforce basic network-level access controls.
- Telemetry and Analytics Engine: The system constantly analyzes the data coming from the endpoints. If a device exhibits anomalous behavior like attempting to download unusually large files or disabling its local firewall, the system flags it or automatically remediates the issue.
Core Components of an Endpoint Management Strategy
A robust endpoint management framework isn't just one tool; it's a collection of integrated disciplines:
- Asset Discovery and Inventory: You cannot protect what you cannot see. The first step is maintaining a real-time ledger of every piece of hardware and software touching your network.
- Access Control and Authentication: Utilizing Multi-Factor Authentication (MFA) and biometric logins to ensure the user behind the keyboard is who they claim to be.
- Patch and Vulnerability Management: Automatically pushing OS updates and third-party software patches during maintenance windows to close known security gaps.
- Application Control: Whitelisting approved applications and blocking malicious or unauthorized software from executing.
Endpoint Management vs. MDM vs. UEM
If you are evaluating tools, you have likely run into an alphabet soup of acronyms. It's helpful to view these as an evolutionary timeline of endpoint management.
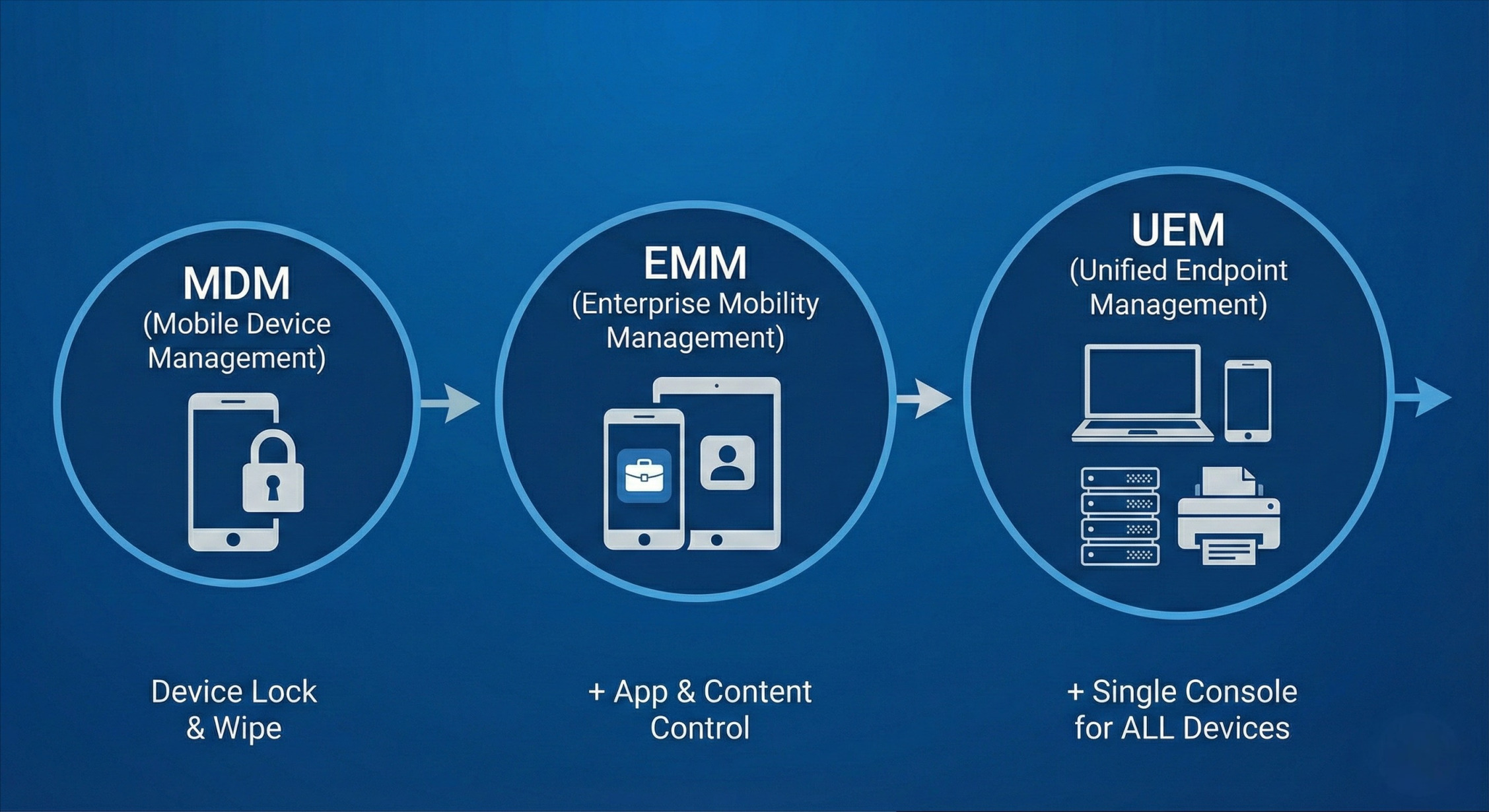
MDM (Mobile Device Management) was the first wave, born out of the smartphone revolution. It focuses strictly on managing mobile devices (phones and tablets). It allows IT to provision devices, enforce passcodes, and remotely wipe data if a device is lost or stolen.
EMM (Enterprise Mobility Management). As mobile work grew more complex, MDM evolved into EMM. EMM goes beyond the hardware layer to manage the content and applications. It introduced Mobile Application Management (MAM) to create corporate app stores and containerization to securely separate personal photos from corporate emails on BYOD phones.
UEM (Unified Endpoint Management) is the modern standard. It rolls MDM, EMM, and traditional PC lifecycle management into one unified platform. Whether you are patching a Windows 11 desktop, updating an Android tablet, or securing a ruggedized warehouse scanner, UEM handles it all from a single console. This eliminates the blind spots created by running disjointed management tools.
Choosing the Right Endpoint Management Solution
Selecting the right platform depends entirely on your architectural needs. When evaluating a UEM or endpoint management tool, look for:
- Broad OS Support: Ensure it supports Windows, macOS, Linux, iOS, Android, and ChromeOS natively.
- Zero Trust Integration: The tool should be able to enforce continuous conditional access based on device health.
- Automation Capabilities: Can it automatically isolate a device if it detects ransomware-like behavior?
- API Extensibility: It should integrate smoothly with your existing IT Service Management (ITSM) tools and Security Information and Event Management (SIEM) systems.
Best Practices for Endpoint Management in 2026
The threat landscape shifts daily. To keep your network locked down without frustrating your end-users, adhere to these modern endpoint management best practices.
1. Implement a Device-Centric Zero Trust Architecture
Gone are the days when connecting to the corporate VPN granted you free rein. Adopt a "never trust, always verify" mindset. Your management system should perform continuous posture validation. Even if a user authenticates successfully, if their laptop's antivirus is disabled or their OS is missing a critical patch, the management system should dynamically restrict their access to sensitive cloud apps until the device is brought back into compliance.
2. Embrace Autonomous Endpoint Management (AEM)
With the sheer volume of devices and alerts, human teams simply can't keep up manually. Leverage platforms that utilize machine learning to establish behavioral baselines. Autonomous systems can self-heal common issues like restarting a crashed VPN client or reinstalling a removed security agent, without generating a helpdesk ticket or requiring human intervention.
3. Enforce the Principle of Least Privilege
Users should only have the administrative rights necessary to do their jobs. By stripping local admin rights from standard users through your endpoint management policies, you drastically reduce the damage malware can do if it sneaks onto a device
4. Secure the BYOD Experience Sensibly
If you allow personal devices, rely heavily on application containerization. Do not manage the entire personal device; manage the corporate data on it. Enforce Data Loss Prevention (DLP) policies that prevent a user from copying text from a secure corporate email app and pasting it into their personal messaging apps.
5. Continuously Audit and Report
Compliance isn't an annual checklist; it's a continuous state. Use your management tools to run daily automated reports on patch density, encryption status (like BitLocker or FileVault), and unauthorized software installations. Identifying a vulnerability before an auditor or a hacker does is the ultimate goal.
Future-Proofing Your Endpoint Management
As hybrid cloud environments grow and AI-driven cyber threats become more sophisticated, your endpoints will remain the most vulnerable battleground. By consolidating your tools into a Unified Endpoint Management platform, automating your patching, and enforcing Zero Trust principles, you transform your endpoints from a security liability into a resilient, productive asset.
Security and management are not one-time projects. They require constant vigilance, adaptation, and a willingness to leverage intelligent automation to stay ahead of the curve. Ultimately, an agile endpoint strategy empowers your workforce to operate seamlessly from anywhere without ever compromising sensitive corporate data. By proactively embracing these advanced frameworks today, you ensure your organization remains both secure and highly competitive tomorrow.
Ready to Secure Your IT Infrastructure?
Navigating the complexities of a modern, distributed workforce doesn't have to be a solo mission. Whether you need to transition to a Unified Endpoint Management (UEM) platform, enforce Zero Trust policies, or automate your patching protocols, we are here to help.
Stop managing devices manually and start scaling securely.















