
What is Network Design? Process, Topologies & Best Practices

To define it simply, network design is the planning, mapping, and implementation phase of a computer network infrastructure. It is a highly technical process executed by network architects and engineers to evaluate, understand, and scope the requirements of an organization before any physical or virtual hardware is deployed.
At its core, network design serves as the blueprint for your IT ecosystem. Just as you wouldn't build a skyscraper without architectural blueprints, you shouldn't deploy an enterprise IT environment without a comprehensive network design. This process evaluates both the physical equipment, such as routers, switches, servers, and cabling, and the logical configuration, including IP addressing schemes, routing protocols, and security policies.
Core Components of Network Design
When asking "what is network design," it is crucial to break it down into its two primary components: physical and logical design.
1. Logical Network Design:
This conceptual phase dictates how data flows through the network. It does not concern itself with specific hardware brands but rather focuses on network topology, IP addressing (IPv4 and IPv6), subnetting, VLAN (Virtual Local Area Network) segmentation, routing protocols (like OSPF or BGP), and access control lists (ACLs).
2. Physical Network Design:
Translating the logical framework into a tangible reality, the physical network design outlines the specific hardware required. It dictates where cables will run, the location of server racks, the specific models of physical routers, switches, and firewalls, and the environmental controls required in the data center
By marrying these two components, a successful network design process creates an IT infrastructure that is both functionally logical and physically robust.
Why is Network Design Important for Businesses?
Understanding what network design is goes beyond technical jargon; it directly translates to business continuity and profitability. Poorly designed networks are expensive. They lead to latency issues, dropped packets, slow application performance, and, worst of all, security breaches.
A deliberate and strategic enterprise network design offers organizations several critical advantages. It minimizes the total cost of ownership (TCO) by preventing over-provisioning, reducing troubleshooting time, and ensuring compliance with data privacy regulations
The Role of Network Design in Scalability and Performance
One of the primary answers to "what is network design meant to achieve?" is scalability. Businesses are not static; they grow, acquire new offices, hire more remote employees, and adopt bandwidth-heavy cloud applications.
A forward-thinking network design anticipates this growth. By implementing modularity and hierarchical frameworks, a network architect ensures that adding new users or locations does not require tearing down the existing infrastructure. Furthermore, network performance is directly tied to design. By optimizing bandwidth allocation, implementing Quality of Service (QoS) for critical traffic like VoIP (Voice over IP), and eliminating network bottlenecks, a solid network design guarantees a seamless end user experience.
Key Phases in the Network Design Process
Executing a successful network design is not a one-step task. It follows a rigorous methodology. The most widely accepted framework in the networking industry is the Top-Down approach, which starts with the application and user needs before moving down to the physical hardware.
Let's break down the critical steps in the network design process.
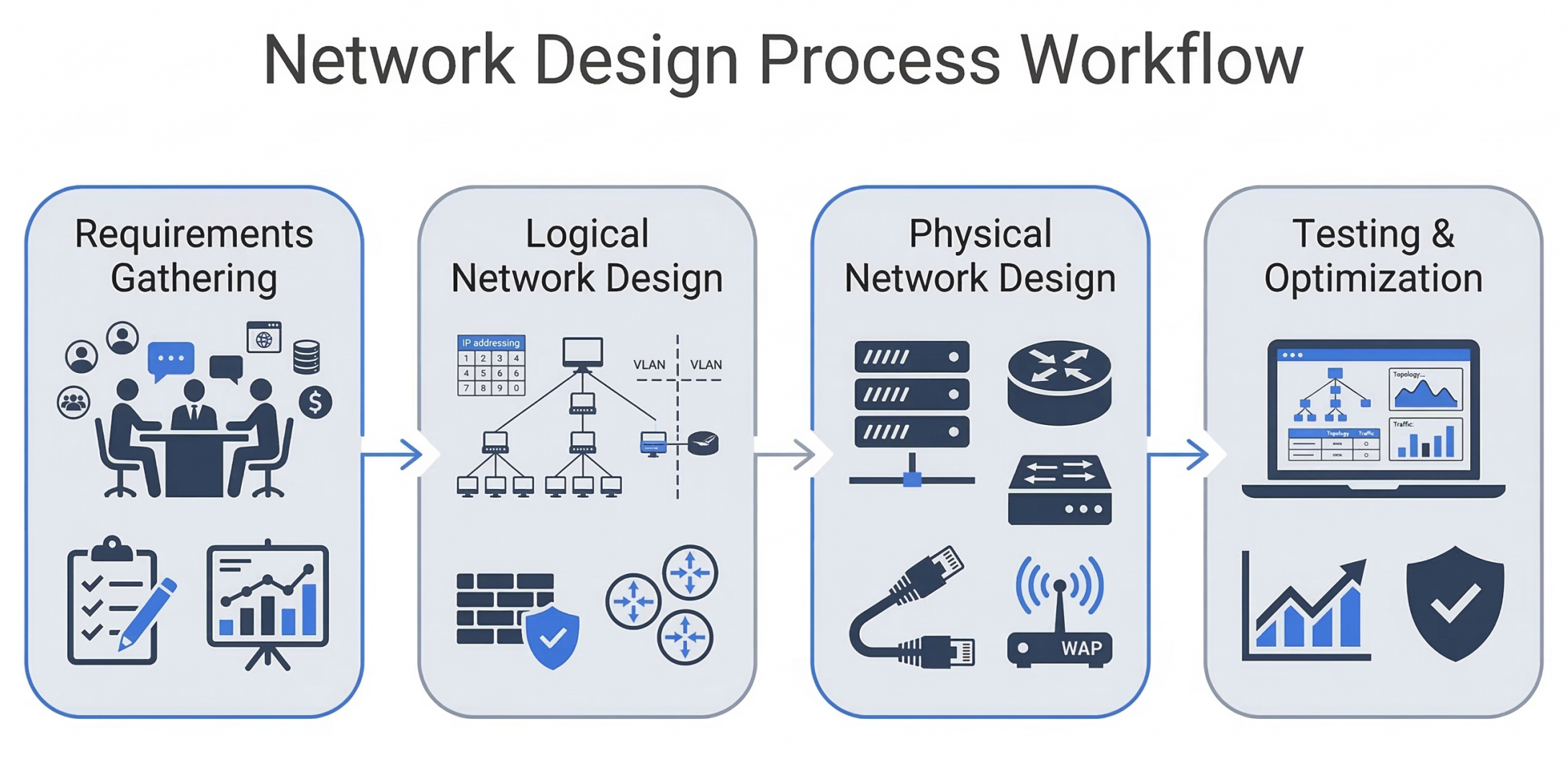
Phase 1: Requirements Gathering and Analysis
You cannot design a network without knowing what it needs to accomplish. The first phase of network design involves intense consultation with business stakeholders. Network engineers must determine the business goals, technical constraints, and operational requirements.
Key questions asked during this phase include:
- How many users will the network support?
- What are the primary applications (e.g., heavy database queries, video conferencing, cloud access)?
- What is the budget for the IT infrastructure? What are the specific compliance and cybersecurity requirements?
- What is the expected growth rate over the next 3 to 5 years?
Phase 2: Logical Network Design
Once the requirements are documented, the logical network design begins. This is where network architects map out the digital pathways of the infrastructure.
During the logical design phase, engineers focus on:
- IP Addressing Strategy: Designing a scalable IP subnetting scheme that prevents IP conflicts and allows for easy routing.
- Routing and Switching Protocols: Deciding whether dynamic routing protocols like EIGRP, OSPF, or BGP are necessary based on the size of the network.
- Network Segmentation: Planning VLANs to separate traffic. For example, keeping guest Wi-Fi traffic entirely separate from corporate financial data.
- Security Architecture: Designing the placement of firewalls, Intrusion Detection Systems (IDS), and outlining Zero Trust network access policies.
Phase 3: Physical Network Design
With the logical map approved, the network design process transitions to the physical phase. Here, abstract concepts become tangible hardware procurement lists.
This phase of network design involves:
- Hardware Selection: Choosing the exact makes and models of routers, core switches, access switches, and Next Generation Firewalls (NGFW).
- Cabling Infrastructure: Deciding between Cat6 copper cabling, fiber optics for long-haul and high-speed core connections, and mapping out the cable runs.
- Wireless Design: Conducting RF (Radio Frequency) site surveys to determine the optimal placement of Wireless Access Points (WAPs) to eliminate dead zones and ensure Wi-Fi coverage.
- Data Center Layout: Designing the physical layout of the server racks, cooling systems, and Uninterruptible Power Supplies (UPS).
Phase 4: Testing and Optimization
The final step in understanding what network design is involves validation. Before deploying the design to a live production environment, it must be thoroughly tested. Network simulators and emulators (like Cisco Packet Tracer, GNS3, or CML) are used to build prototype networks.
Engineers will stress-test the design to see how it handles maximum traffic loads, simulate hardware failures to ensure redundancy protocols work, and run penetration tests to validate the security posture. Only after passing these rigorous tests is the network design ready for real-world implementation.
Essential Network Design Principles and Best Practices
To create a resilient and efficient IT infrastructure, network architects adhere to a strict set of industry-standard principles. If you are learning how to design a secure network, mastering these concepts is non-negotiable.
The most common framework used globally is the Hierarchical Network Design Model, pioneered by Cisco. This model divides the network into three distinct layers, each with a specific role:
- The Core Layer: The high-speed backbone of the network, designed to switch packets as fast as possible between different sites or data centers.
- The Distribution Layer: The smart layer where routing, filtering, and QoS policies are applied. It aggregates traffic from the access layer before sending it to the core.
- The Access Layer: Where end devices (PCs, printers, IP phones) connect to the network.
Designing for High Availability and Redundancy
A critical aspect of what is network design is ensuring maximum uptime. Network redundancy is the practice of adding duplicate physical devices, links, and logical protocols to prevent a single point of failure.
Best practices for enterprise network design dictate that if a core router fails, a backup router should take over instantly without the user noticing. This is achieved through protocols like HSRP (Hot Standby Router Protocol) or VRRP (Virtual Router Redundancy Protocol). Similarly, physical links between switches are bundled together using LACP (Link Aggregation Control Protocol) so that if one cable is cut, traffic instantly reroutes over the remaining cables, maintaining high availability.
Integrating Network Security from the Ground Up
In modern architectures, security cannot be an afterthought bolted onto the network; it must be deeply woven into the network design itself.
A secure network design incorporates:
- Defense-in-Depth: Layering security mechanisms (firewalls, endpoint protection, email gateways) so that if one fails, others stand in the way.
- Zero Trust Architecture: Never trusting any device by default, whether it is inside or outside the corporate perimeter. Every user and device must be authenticated and authorized.
- Micro-segmentation: Dividing the network into tiny, isolated zones to prevent lateral movement by malicious actors. If malware infects a workstation in the marketing VLAN, micro-segmentation ensures it cannot easily spread to the database server VLAN.
Types of Network Design Topologies
When answering "what is network design," one must discuss network topologies. The topology is the geometric arrangement of the network, dictating how nodes (devices) are connected to one another.
The choice of topology drastically impacts network performance, cost, and complexity.
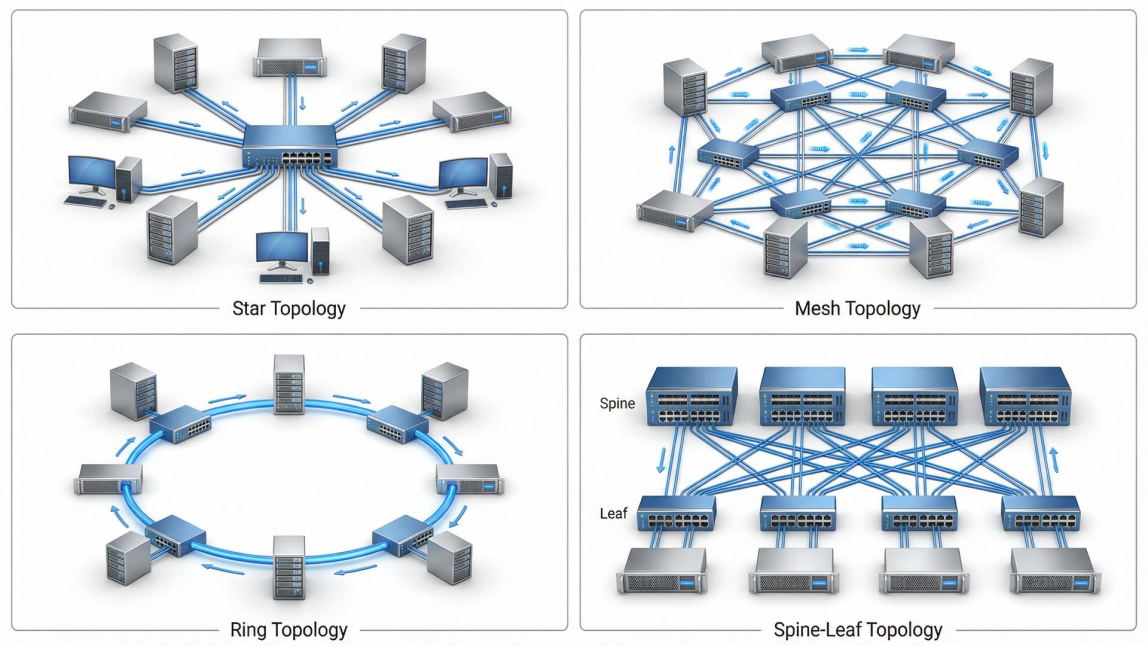
Star, Mesh, Ring, and Hybrid Network Design
- Star Topology: The most common topology in modern LAN (Local Area Network) environments. Every device connects to a central hub or switch. It is easy to manage and troubleshoot, but the central switch represents a single point of failure (which is why redundancy is vital).
- Mesh Topology: Used heavily in WAN (Wide Area Network) design and wireless networks. In a full mesh network, every node connects to every other node, offering unparalleled redundancy but at a very high cost and complexity. Partial mesh is a more cost-effective compromise.
- Ring Topology: Historically used in older networks (like Token Ring), devices are connected in a closed-loop circle. While largely obsolete in local networks, ring topologies are still utilized in robust fiber-optic WAN links for municipal networks (like SONET rings).
- Spine-and-Leaf Topology: The modern standard for data center network design. It replaces the traditional three-tier hierarchical model with a two-tier structure that drastically reduces latency for server-to-server (east-west) traffic, making it ideal for cloud computing and virtualization environments.
Future Trends Shaping Enterprise Network Design
The field of IT infrastructure is constantly evolving. To fully grasp what network design is today, one must look at the technologies that will define tomorrow. Traditional, rigid, hardware-heavy networks are rapidly giving way to agile, software driven solutions.
Software-Defined Networking (SDN) and Cloud Network Design
The biggest revolution in recent years is Software-Defined Networking (SDN). SDN decouples the network's control plane (the "brains" making routing decisions) from the data plane (the hardware moving the packets). This allows network administrators to manage, program, and secure the entire network centrally via software, rather than configuring each router individually.
Furthermore, as businesses migrate to the cloud, Cloud Network Design has become a primary focus. Designing a network today means integrating on-premise infrastructure with public clouds like AWS, Microsoft Azure, or Google Cloud. This requires designing secure VPN tunnels, utilizing AWS Direct Connect or ExpressRoute, and ensuring seamless traffic flow between physical offices and virtual data centers.
Another major trend is the adoption of SD-WAN (Software-Defined Wide Area Network). SD-WAN optimizes WAN network design by dynamically routing traffic over multiple connection types (MPLS, broadband, 5G) based on real-time network performance, saving enterprises thousands of dollars in telecom costs while boosting application performance.
Lastly, the rise of SASE (Secure Access Service Edge) is fundamentally altering how we view network security design. SASE converges SD-WAN capabilities with comprehensive cloud-native security functions (like Cloud Access Security Brokers, Secure Web Gateways, and Zero Trust Network Access) to securely connect users to applications, regardless of their location.
Conclusion: Mastering What is Network Design
Ultimately, network design is the strategic process of planning and building the digital backbone of an organization. It involves analyzing business requirements, creating logical architectures, and selecting the right hardware, protocols, and technologies to ensure a reliable and efficient network infrastructure. Each stage from requirements gathering to deployment plays a critical role in maintaining the performance, stability, and security of enterprise IT environments. A strong network design emphasizes scalability, high availability, robust security, and the ability to adapt to modern technologies like software-defined networking (SDN) and cloud computing.
For organizations aiming to strengthen their IT infrastructure, understanding these principles is essential to building networks that are secure, resilient, and future-ready. At AS13.AI, we help businesses design scalable, cloud-ready, and high-performance network architectures tailored for modern enterprise environments.















